Who doesn't love a good "Whodunit" story? The popular CSI-style crime drama appeals to our human nature, piquing curiosity and replaying the endless battle of good versus evil. But in reality, dealing with crime, security and forensics matters can be tedious and time-consuming. This is distinctly true in the area of network security, as revealed in a recent study tracking the most pressing trends facing network professionals worldwide.
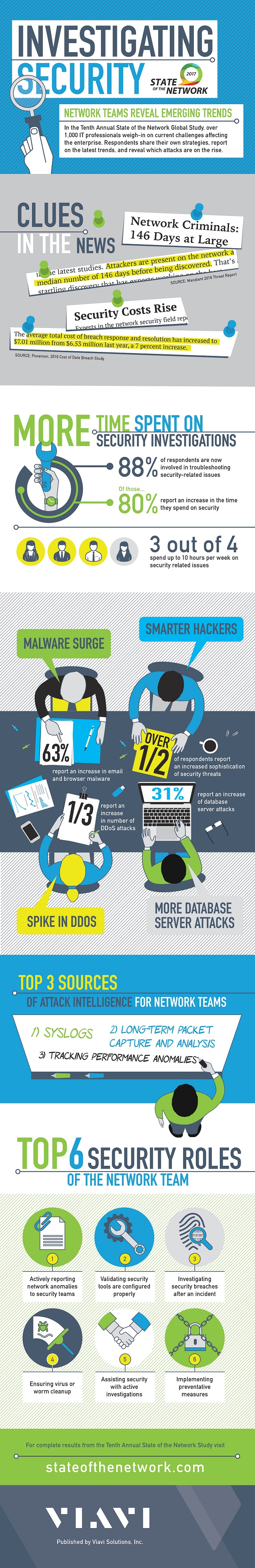
According to the tenth annual State of the Network study from Viavi, nearly 90 percent of respondents say they are involved in troubleshooting security-related issues, with 80 percent reporting the time consumed by these issues has increased in the past year. Considering the risk of damaging media coverage when high-profile breaches occur, it's not too surprising that security teams enlist help to bolster network defenses and investigate attacks.
In fact, security is already the number one spending priority for most CIOs, with billions spent each year on firewalls, intrusion detection systems and other preventative security measures. Global spending on information security is expected to reach $90 billion this year, and around 80 percent of CIOs anticipate spending even more on security technology in the near future.
Unfortunately, escalating data traffic is only likely to make matters worse. More than half of the roughly 1,000 CIOs, IT directors and network engineers surveyed expect their organization's bandwidth consumption to grow by up to 50 percent in the next 12 months. That means a lot more data traffic that could be hiding malware or ransomware flowing through their networks.
But it's not just a matter of dealing with more data traffic and an increasing number of threats; the nature and severity of security threats is changing as well. In the past year alone, 63 percent of IT pros identified an increase in email and browser-based malware attacks, while 52 percent cite heightened threat sophistication. Nearly one in three study respondents also report a surge in distributed denial of service (DDoS) attacks, such as the recent Mirai botnet attacks which have become increasingly severe.
Revealing Evidence
Yes, it's true that dealing with network security can be time-consuming, adding to an already full schedule managing network upgrades, cloud migration and big data initiatives … not to mention integrating technologies like VoIP and software-defined networking (SDN). But the alternative of leaving your network open to an attack is not an option. Vigilance is the new normal.
Staying a step ahead of network security threats requires real-life sleuthing, not too dissimilar from popular pulp fiction detectives. Regular network performance monitoring (NPM) helps IT pros recognize abnormal traffic, which is critical for pinpointing an ongoing attack or security issue. For many network teams, syslogs are the primary method of detecting possible security issues, while others track network performance anomalies.
Nearly a quarter of the State of the Network respondents use NPM tools that enable long-term packet capture and analysis to keep a watchful eye on their networks. This type of technology enables forensic data collection with retrospective analysis to research the origin and extent of an attack — important data given that it now takes IT teams an average of 146 days to identify threats lurking on their network.
One of the key challenges of NPM today is the need to monitor network activity across hybrid network environments. This issue is becoming particularly complex as applications are now routinely spanning both physical and virtual environments, including on-premise servers, private clouds and public clouds. Greater visibility into all the network traffic is necessary to understand what's normal behavior, and what isn't normal, in order to make quick policy changes like blocking potentially malicious IP addresses and traffic.
Despite this fragmented environment, enterprises can go a long way toward advancing network security by fostering effective collaboration between network and security teams, including documented workflows and integrated forensics and performance management tools. Because after all, both teams are probably looking at the same anomaly at the same time. A decisive verdict of security threat or network performance issue should be based on hard facts, not circumstantial evidence.