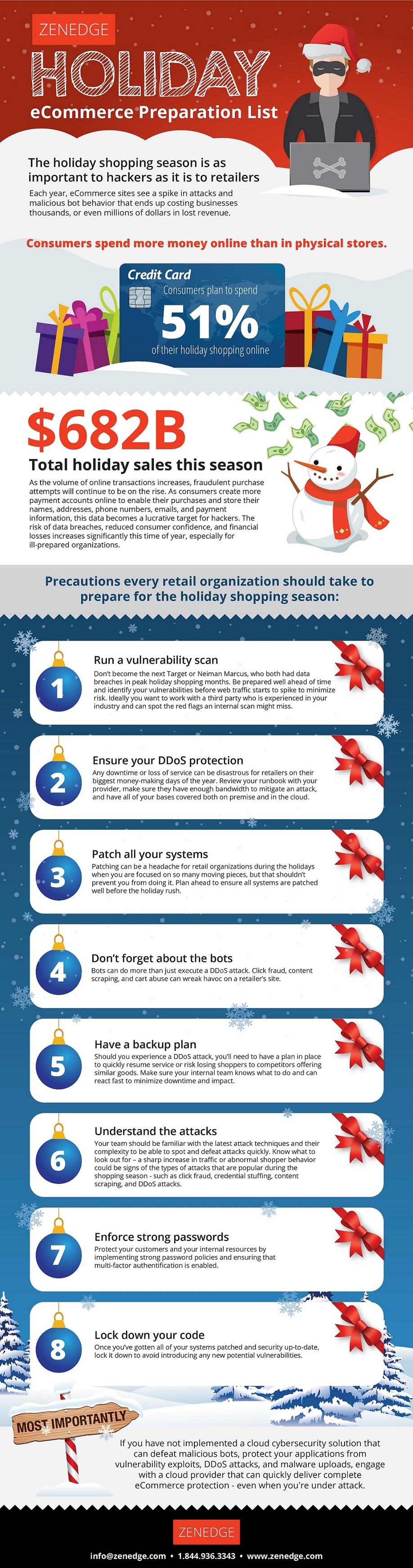
As the 2017 holiday shopping season gets under way, with sales expected to hit $682 billion, this year could be the first that consumers spend more online than in stores. In fact, they may spend more than half of their holiday dollars online this year. As more people flock to e-commerce sites than ever before, the potential threat to retailers from hackers increases exponentially.
As the volume of online transactions rises, fraudulent purchase attempts, denial of service (DoS) attacks and detrimental bot behavior spike, leaving retailers at risk of losing thousands, or even millions, in revenue on their busiest money making days of the year and could leave their reputations in shambles. Just think back to Target and Neiman Marcus who had breaches in peak holiday season.
Due to the massive data breaches reported this year, whereby hundreds-of-millions of identities were stolen, hackers and their bot armies are positioned quite well for a lucrative holiday season. Expect significant increases in counterfeit purchasers using fraudulent credit cards. In addition, hackers and their bot armies are likely to repetitively make and cancel purchases, hold and/or consume inventory, scrape sites, steal information, and a host of other unwanted activities. Since this is the time of year when retailers experience significant increases in sales (as compared to the rest of the year), it's imperative for retailers to take these threats serious, and plan for the worst.
Hacking tools are increasingly more available, DDoS botnets made up of infected IoT are growing in size and firepower, and launching cyberattacks are getting cheaper by the minute. There are more outfits in Russia, China, and elsewhere hacking for their own financial gain, and others are readily available for hire for lower costs than seen previously. The global political landscape, domestic discontent, and heightened security concerns will likely increase consumers' online purchases vs. going to malls and other physical outlets. This holiday season will be the perfect time to for hackers to target and disrupt the shopping season, creating havoc and causing chaos. Damages and losses could very well be at an all time high.
In order to combat these behaviors, see the checklist of precautions every retailer should keep in mind to prepare ahead of the holiday rush, including running a vulnerability scan, patching all systems, ensuring DoS protection, implementing a backup plan and understanding the potential attacks and your vulnerabilities, among other preparations.