ExtraHop Networks introduced a new monitoring bundle that provides cross-tier visibility for Microsoft SharePoint 2010 and SharePoint 2013 environments.
The SharePoint monitoring bundle enables IT teams to proactively monitor and troubleshoot problems without requiring any preconfiguration or invasive agents.
With 180 million people relying on SharePoint collaboration software every day, it has never been more important for IT teams to ensure that the SharePoint environment is running smoothly. Traditional monitoring tools, however, do not provide IT Operations teams with correlated visibility across the entire SharePoint application delivery chain. As a result, when SharePoint users complain about slow performance or downtime, IT Operations teams are left blind to the exact source of the problem.
ExtraHop’s new SharePoint monitoring bundle — available free of charge on the ExtraHop customer forum — solves this problem by tracking and correlating every SharePoint transaction as it passes from the user, to the web server, back and forth between the web server and database, and across the network.
The ExtraHop platform recognizes SharePoint transactions by the globally unique identifier (GUID) that SharePoint attaches to individual transactions. This passive recognize-and-trace method of transaction tracing requires no configuration and is a less expensive and less complex alternative to the tag-and-trace method that requires agents to be installed on systems.
Downloading and implementing the SharePoint monitoring bundle takes just minutes, with immediate benefits:
- Monitor the entire application delivery chain for SharePoint, including the client or browser, web servers, DNS, Active Directory, firewall devices, load balancers, SharePoint servers, Microsoft SQL Server database servers, and storage systems
- Distinguish between transaction latency at the web and database tiers
- Distinguish between network transfer time and server processing time within each tier
- Capture extensive application-level details for each transaction, such as specific errors and the methods used
- Create geographic visualizations of SharePoint activity, including the location of devices generating errors, with the ExtraHop Geomaps and Application Activity Map features
“Social enterprises that rely on SharePoint need to keep those environments up and running with low latency,” said Dennis Callaghan, Senior Enterprise Software Analyst with 451 Research. “ExtraHop’s turnkey SharePoint monitoring bundle delivers a holistic view of the application delivery chain and drills down to the granular transaction details to pinpoint the root cause of problems that can impact the end user’s experience of SharePoint. What makes this offering especially compelling is that it works out of the box and does not require agents to be installed on systems.”
“Our SharePoint monitoring bundle highlights one of the key advantages of the ExtraHop platform, which is its flexibility to meet the varied demands of real-world IT environments,” says Jesse Rothstein, CEO, ExtraHop. “Users create and share monitoring bundles on our forum, and we add some of our own, such as the SharePoint bundle. These bundles are extensible so that users can easily modify and add to them as needed. We’re proving how ExtraHop is an open platform for operational intelligence. We have the technology in place—our documented API, Application Inspection Triggers, rsyslog export, and more — and our user community is making this vision a reality.”
The ExtraHop SharePoint solution bundle is available now on all versions of the ExtraHop platform and users can try it free for 60 days by downloading the ExtraHop Discovery Edition.
The Latest
As enterprises accelerate their cloud adoption strategies, CIOs are routinely exceeding their cloud budgets — a concern that's about to face additional pressure from an unexpected direction: uncertainty over semiconductor tariffs. The CIO Cloud Trends Survey & Report from Azul reveals the extent continued cloud investment despite cost overruns, and how organizations are attempting to bring spending under control ...

According to Auvik's 2025 IT Trends Report, 60% of IT professionals feel at least moderately burned out on the job, with 43% stating that their workload is contributing to work stress. At the same time, many IT professionals are naming AI and machine learning as key areas they'd most like to upskill ...
Businesses that face downtime or outages risk financial and reputational damage, as well as reducing partner, shareholder, and customer trust. One of the major challenges that enterprises face is implementing a robust business continuity plan. What's the solution? The answer may lie in disaster recovery tactics such as truly immutable storage and regular disaster recovery testing ...
IT spending is expected to jump nearly 10% in 2025, and organizations are now facing pressure to manage costs without slowing down critical functions like observability. To meet the challenge, leaders are turning to smarter, more cost effective business strategies. Enter stage right: OpenTelemetry, the missing piece of the puzzle that is no longer just an option but rather a strategic advantage ...
Amidst the threat of cyberhacks and data breaches, companies install several security measures to keep their business safely afloat. These measures aim to protect businesses, employees, and crucial data. Yet, employees perceive them as burdensome. Frustrated with complex logins, slow access, and constant security checks, workers decide to completely bypass all security set-ups ...

In MEAN TIME TO INSIGHT Episode 13, Shamus McGillicuddy, VP of Research, Network Infrastructure and Operations, at EMA discusses hybrid multi-cloud networking strategy ...
In high-traffic environments, the sheer volume and unpredictable nature of network incidents can quickly overwhelm even the most skilled teams, hindering their ability to react swiftly and effectively, potentially impacting service availability and overall business performance. This is where closed-loop remediation comes into the picture: an IT management concept designed to address the escalating complexity of modern networks ...
In 2025, enterprise workflows are undergoing a seismic shift. Propelled by breakthroughs in generative AI (GenAI), large language models (LLMs), and natural language processing (NLP), a new paradigm is emerging — agentic AI. This technology is not just automating tasks; it's reimagining how organizations make decisions, engage customers, and operate at scale ...
In the early days of the cloud revolution, business leaders perceived cloud services as a means of sidelining IT organizations. IT was too slow, too expensive, or incapable of supporting new technologies. With a team of developers, line of business managers could deploy new applications and services in the cloud. IT has been fighting to retake control ever since. Today, IT is back in the driver's seat, according to new research by Enterprise Management Associates (EMA) ...
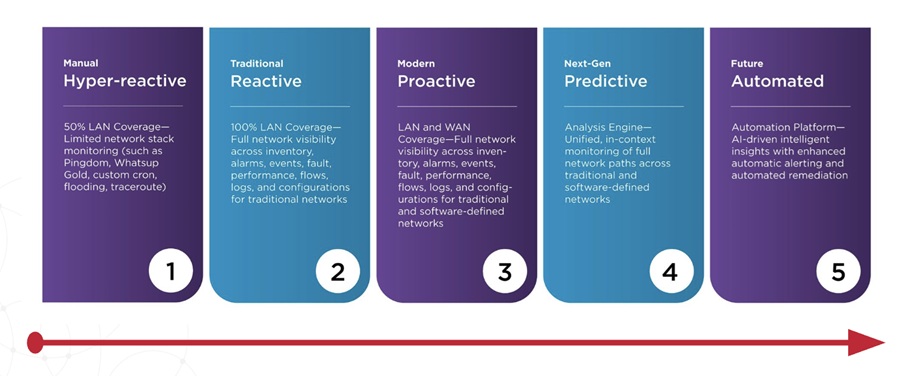
In today's fast-paced and increasingly complex network environments, Network Operations Centers (NOCs) are the backbone of ensuring continuous uptime, smooth service delivery, and rapid issue resolution. However, the challenges faced by NOC teams are only growing. In a recent study, 78% state network complexity has grown significantly over the last few years while 84% regularly learn about network issues from users. It is imperative we adopt a new approach to managing today's network experiences ...