The internet is generally said to have been born in 1989, and since then, every 11 years, there have been significant changes to core networking technology. Why? Because as enterprise networks grew, they required additional scale, speed, reliability, security, and privacy.
The first shift was from frame relay and IP over ATM to MPLS in the early 2000s. MPLS provided better performance, reliability, and security. Next was the shift to SD-WAN in 2012. SD-WAN dramatically lowered costs and provided much-needed agility.
So, 11 years later, we're due for a big shift — but to what? To find out, Graphiant commissioned the 2023 State of Network Edge survey. The findings do, in fact, point to an eminent shift.
Rise of New Networking Use Cases
Providing connectivity between all enterprise resources (data center, branch offices, factories, and employees) has always been a primary use case for the network.
But respondents reported the rise of two important network use cases:
■ Connecting to partner or customer networks
■ Connecting to cloud(s)
These use cases started to rise three years ago, and by three years from now, they will join connecting enterprise resources as the top use cases enterprises must solve.
Building Edge Networks is Difficult
Interestingly, these three use cases are also the ones respondents rated the most difficult to handle.

Three reasons are driving this difficulty:
■ Scale. Enterprises now connect to more nodes than ever. For example, enterprises now connect to remote employees, partners, customers, and multiple clouds.
■ Security & Privacy. Traffic routinely travels through a digital wilderness over which IT has no visibility or control.
■ Agility. MPLS takes 3 to 6 months to provision. SD-WAN requires IT to set up an enormous number of tunnels. But enterprises cannot wait. Connections are now provisioned at the speed of business. Months need to become hours or minutes.
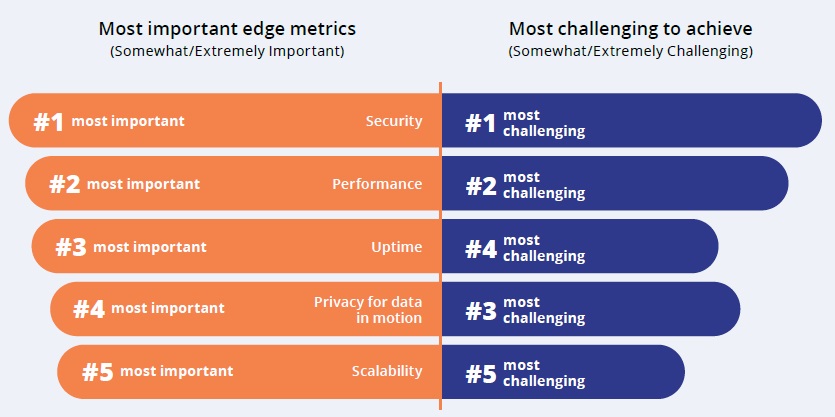
The Most Important Objectives are also the Most Challenging
The metrics most important to enterprises are also the most challenging to achieve — security, performance, uptime, privacy, and scalability. Unfortunately, these are also the hardest to achieve.
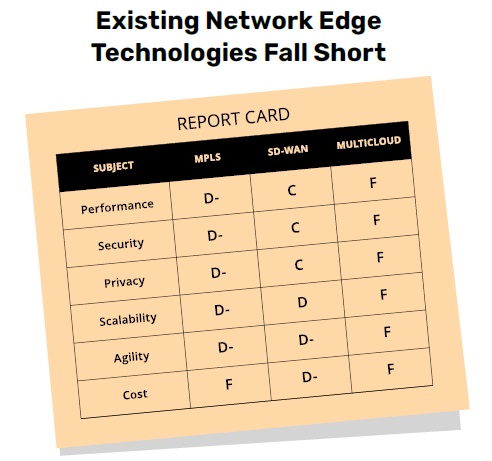
The reason? Existing networking technology is failing at delivering these. Respondents gave MPLS, SD-WAN, and multicloud technologies failing grades, especially with agility and cost.
Is Network-as-a-Service the Answer?
Network-as-a-Service (NaaS) holds promise. It is extremely agile to provision (as is typical of as-a-Service solutions). Would network architects and admins consider an as-a-Service solution if a NaaS solution can also nail performance and security/privacy?
Before we answer that question, it's helpful to see the extent to which enterprises have adopted other classes of as-a-Service solutions. In fact, the adoption of as-a-Service has been robust.
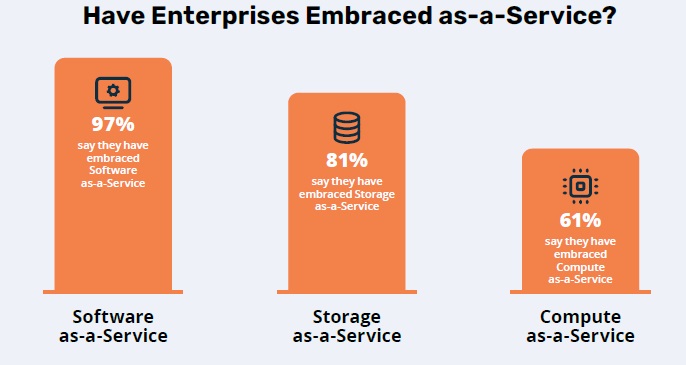
Nearly everyone uses SaaS, and most use Storage- and Compute-as-a-Service.
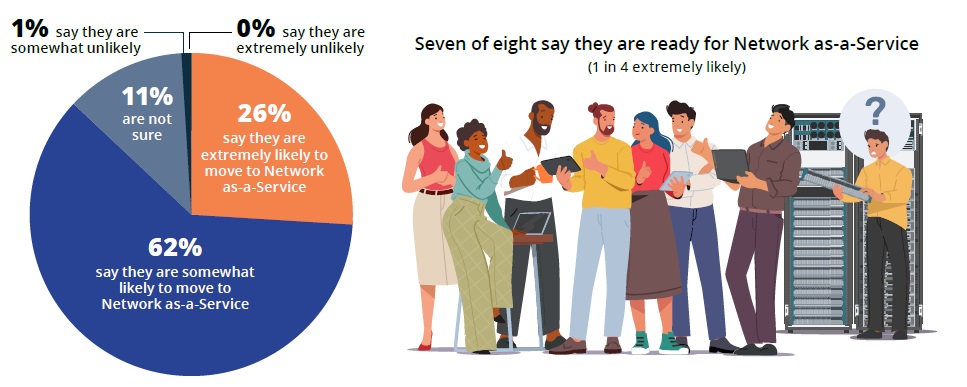
As for NaaS, seven in eight respondents say they are likely to move to NaaS. In fact, one in four say they are extremely likely.
How to Move to NaaS
Which leaves the last question — how can enterprises prepare for NaaS? Here are three questions to consider:
1. What are your goals, and is your current solution delivering what you need to your customers? Is it security, performance, privacy, scalability, agility, or cost savings that you need to focus on?
In the long term, how much cost savings are there in building bespoke networks?
2. Can your enterprise continue to build enough bespoke networks to accommodate these types of use cases over the next 3 years?
Have you considered Network as-a-Service for your business? We live in a dynamic world where more connections are needed, and the next phase in next-gen connectivity is to consume the network.
3. How effectively are you addressing the following use cases: connectivity between all enterprise resources, connectivity with all the public clouds the enterprise uses, and connectivity with external organizations? Is it possible to engage expert assistance to help in your quest for network sovereignty?
Legacy models of connectivity don't work anymore, especially in the modern world. You need to control the network before it controls you. This new world focuses on a modern world where enterprises can take back control of their network before their network controls them — all through a new business model where enterprises would only need to consume the network instead of building it.
Methodology: Eleven Research surveyed 200 network architects and network admins from large enterprises in North America. The respondents were senior, director, VP and C-level IT managers. Eleven Research chose respondents who spent at least 50% of their time designing, provisioning, and managing the network edge.
